- Library ›
- IT & Data Center ›
- IT Infrastructure Audit Checklist
IT Infrastructure Audit Checklist
Inventory Management
Maintenance Records
Performance Metrics
Upgrade Needs
Licencing Compliance
Security Measures
Usage Review
Version Control
Configuration Management
Connectivity Tests
Security Protocols
Access Controls
Backup Verification
Data Inventory
Security Audits
Plan Review
Recovery Point Objectives
Recovery Time Objectives
Simulation Tests
Support Ticket Analysis
Training Programs
User Feedback
Documentation Review
Policy Enforcement
Regulatory Checklist
Is this sample what you are looking for?
Sign up to use & customise this template, or create your own custom checklist:
Checklist by GoAudits.com – Please note that this checklist is intended as an example. We do not guarantee compliance with the laws applicable to your territory or industry. You should seek professional advice to determine how this checklist should be adapted to your workplace or jurisdiction.
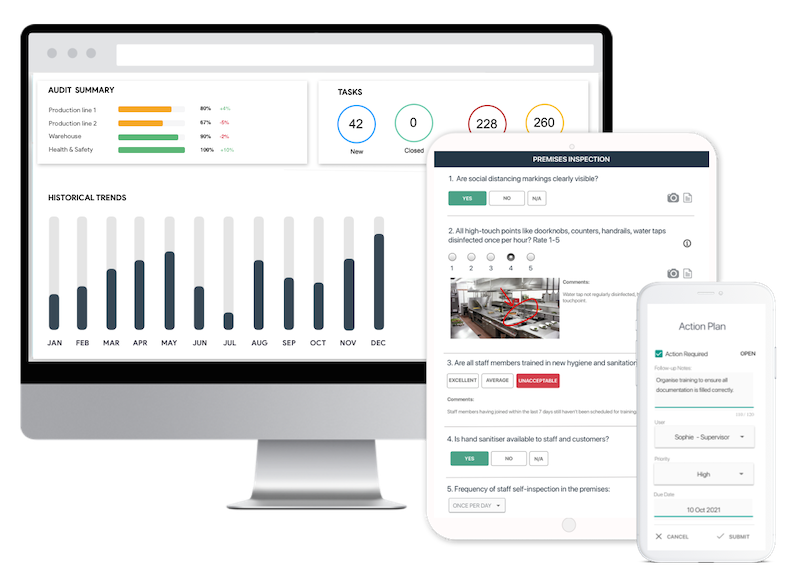
Easy inspection app for your digital checklists
- Conduct inspections anytime, anywhere - even offline
- Capture photos as proof of compliance or areas needing attention
- Instantly generate and share detailed reports after the inspections
- Assign & track follow-up tasks, view historical trends on a centralized dashboard