- Library ›
- ISO Standards ›
- ISO 27001 Checklist
ISO 27001 Checklist
Management Direction For Information Security
Information Security Roles And Responsibilities
Mobile Devices And Teleworking
During Employment
Prior To Employment
Termination And Change Of Employment
Information Classification
Media Handling
Responsibilities For Assets
Responsibilities For Assets
System And Application Access Control
User Responsibilities
Cryptographic Controls
Equipment
Secure Areas
Control Of Operational Software
Information Systems Audit Considerations
Logging And Monitoring
Operational Procedures And Responsibilities
Protection From Malware
System Backup
Technical Vulnerability Management
Information Transfer
Network Security Management
Security In Development And Support Processes
Security Requirements Of Information Systems
Suppliers Relationships
Information Security Management
Information Security Continuity
Compliance With Legal And Contractual Requirements
Independent Review Of Information Security
Is this sample what you are looking for?
Sign up to use & customise this template, or create your own custom checklist:
Checklist by GoAudits.com – Please note that this checklist is intended as an example. We do not guarantee compliance with the laws applicable to your territory or industry. You should seek professional advice to determine how this checklist should be adapted to your workplace or jurisdiction.
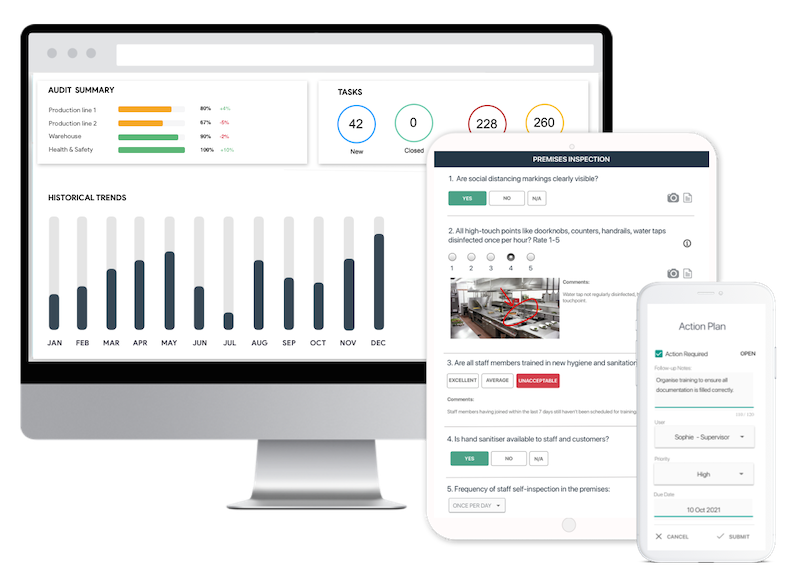
Easy inspection app for your digital checklists
- Conduct inspections anytime, anywhere - even offline
- Capture photos as proof of compliance or areas needing attention
- Instantly generate and share detailed reports after the inspections
- Assign & track follow-up tasks, view historical trends on a centralized dashboard